Strategic planning requires more than just identifying what an organization does well. It demands a clear-eyed view of what could go wrong. The SWOT analysis is a foundational tool for this purpose, specifically the Threats quadrant. However, identifying a threat is only the first step. The real value lies in transforming those identified threats into a robust Risk Management Plan. This guide provides a comprehensive framework for converting SWOT findings into actionable defense strategies without relying on specific software or tools.
🧐 Understanding the ‘T’ in SWOT: Threat Identification
In the context of strategic planning, Threats are external factors outside the control of the organization that could cause trouble for the business or project. Unlike weaknesses, which are internal, threats exist in the market, the regulatory environment, or the competitive landscape. To derive a risk management plan, one must first understand the nature of these threats.
Types of External Threats
Threats generally fall into several distinct categories. Recognizing the category helps in determining the appropriate response strategy.
- Market Shifts: Changes in consumer behavior or economic downturns that reduce demand.
- Competitive Pressure: New entrants, price wars, or superior technology from rivals.
- Regulatory Changes: New laws, compliance requirements, or trade restrictions.
- Technological Obsolescence: Rapid advancements that make current methods outdated.
- Supply Chain Disruptions: Dependencies on vendors that may fail or increase costs.
- Reputational Risks: Public perception issues stemming from industry events or past actions.
📊 Connecting Threats to Risk Categories
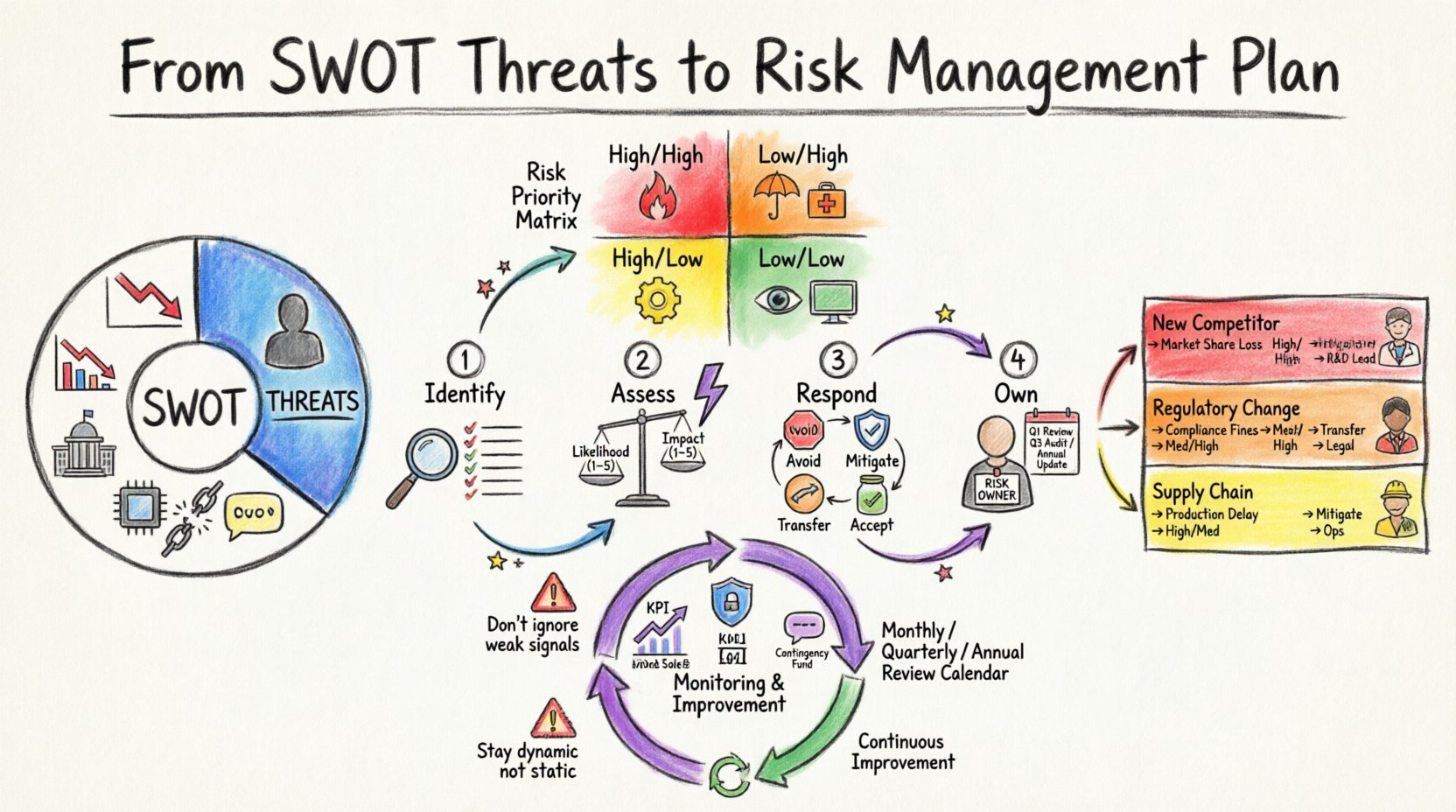
Not all threats carry the same weight. A Risk Management Plan requires prioritization. This is where the translation from “SWOT Threat” to “Risk Item” occurs. A threat becomes a risk when there is a probability of occurrence and a potential impact on objectives.
The Probability and Impact Matrix
To structure the data effectively, organizations often use a matrix. This visual tool helps in categorizing risks into high, medium, and low priority buckets.
- High Probability / High Impact: These are critical risks. They require immediate attention and dedicated resources.
- Low Probability / High Impact: These are catastrophic scenarios (e.g., natural disasters). They require contingency planning.
- High Probability / Low Impact: These are operational annoyances. They require process adjustments.
- Low Probability / Low Impact: These are monitored but do not require active mitigation.
🛠️ Step-by-Step: Building the Plan
Creating a plan involves a systematic workflow. This process ensures that no threat is overlooked and that every identified risk has a designated owner and response strategy.
Step 1: Risk Identification
Begin by extracting the Threats from the SWOT analysis. Review each item and ask, “What is the specific risk associated with this?” For example, a threat listed as “New Competitor Entry” becomes a risk of “Market Share Loss”.
- List every threat identified in the SWOT session.
- Clarify the exact nature of the risk.
- Define the scope of the risk (departmental, organizational, project-level).
Step 2: Risk Assessment
Once identified, evaluate the severity. This assessment should be quantitative where possible and qualitative where necessary.
- Likelihood: How probable is the threat to materialize? (1-5 Scale)
- Impact: What is the financial or operational cost if it happens? (1-5 Scale)
- Velocity: How quickly will the risk affect the organization once it occurs?
Step 3: Risk Response Planning
This is the core of the plan. For each risk, select a response strategy. There are four primary approaches to handling risk.
- Avoid: Change the plan to eliminate the threat entirely.
- Mitigate: Take actions to reduce the probability or impact of the threat.
- Transfer: Shift the risk to a third party (e.g., insurance, outsourcing).
- Accept: Acknowledge the risk and prepare to deal with the consequences if it occurs.
Step 4: Ownership and Accountability
A risk cannot be managed if no one is responsible for it. Assign a Risk Owner for every item on the list. This person is accountable for monitoring the risk and executing the response plan.
- Name the specific individual or role.
- Define their specific duties.
- Set review frequencies (weekly, monthly, quarterly).
🔄 Response Strategies for Identified Risks
Understanding the strategy is one thing; executing it is another. Below is a breakdown of how to apply these strategies to common SWOT threats.
1. Avoidance Strategies
Use this when the risk is unacceptable. The goal is to remove the condition that creates the risk.
- Deciding not to launch a product in a volatile market.
- Exiting a region with unstable political conditions.
- Refusing to partner with a supplier with a poor compliance record.
2. Mitigation Strategies
This is the most common approach. You cannot eliminate the risk, but you can reduce it to an acceptable level.
- Implementing dual-sourcing for critical components to prevent supply chain failure.
- Conducting regular cybersecurity training to reduce human error.
- Diversifying revenue streams to buffer against market fluctuations.
3. Transfer Strategies
Outsourcing the risk to an entity better equipped to handle it.
- Purchasing liability insurance.
- Using fixed-price contracts to shift cost overruns to vendors.
- Hiring specialized consultants for high-risk technical tasks.
4. Acceptance Strategies
Some risks are too small to justify the cost of mitigation. Acceptance requires a contingency fund or plan.
- Setting aside a budget reserve for minor cost variances.
- Documenting the decision to accept a minor regulatory risk.
- Monitoring a low-priority threat for changes in probability.
📋 Sample Risk Register Structure
To maintain clarity, a structured table is essential for tracking risks derived from SWOT threats. Below is an example of how to organize this information.
| SWOT Threat | Associated Risk | Likelihood | Impact | Response Strategy | Owner |
|---|---|---|---|---|---|
| New Competitor Entry | Loss of Market Share | High | High | Mitigate (Innovation) | Head of R&D |
| Regulatory Changes | Compliance Fines | Medium | High | Transfer (Insurance) | Legal Counsel |
| Supply Chain Disruption | Production Delays | High | Medium | Mitigate (Stockpiling) | Operations Lead |
| Economic Recession | Reduced Revenue | Medium | Medium | Accept (Cost Control) | CFO |
| Technology Obsolescence | Reduced Efficiency | Low | Low | Mitigate (Training) | IT Manager |
📈 Implementing and Monitoring Controls
A plan is useless if it sits on a shelf. Implementation requires integration into daily operations. This involves setting up control mechanisms and regular check-ins.
Key Performance Indicators (KPIs)
Define metrics that signal when a risk is materializing. These are called Key Risk Indicators (KRIs).
- If the threat is “Competitor Price Cuts”, the KRI might be “Change in Our Sales Volume”.
- If the threat is “Data Breach”, the KRI might be “Number of Failed Login Attempts”.
- If the threat is “Staff Turnover”, the KRI might be “Exit Interview Feedback Frequency”.
Review Cycles
Risk environments change. What was low risk yesterday might be high risk today. Establish a schedule for review.
- Monthly Reviews: For high-priority risks with active mitigation.
- Quarterly Reviews: For standard risks within the operational scope.
- Annual Reviews: For long-term strategic risks and the SWOT analysis itself.
🚫 Common Pitfalls to Avoid
Even with a solid framework, organizations often stumble. Awareness of common mistakes helps in maintaining the integrity of the plan.
- Ignoring Weak Signals: Focusing only on immediate threats while missing gradual trends.
- Confusing Symptoms with Causes: Addressing the visible effect rather than the root threat.
- Lack of Communication: Keeping risk data siloed within one department.
- Over-Reliance on Historical Data: Assuming past performance predicts future threats.
- Static Planning: Treating the plan as a one-time document rather than a living process.
- Resource Misallocation: Spending too much effort on low-impact risks while ignoring high-impact ones.
🧩 Integrating with Broader Strategy
The Risk Management Plan should not exist in a vacuum. It must align with the overall strategic goals of the organization. This ensures that risk mitigation does not hinder growth.
Alignment with Objectives
Ensure that risk responses support the mission. For instance, if the strategy is rapid expansion, risk responses should focus on scalability and speed, not just stability.
- Review strategic goals against the risk register annually.
- Adjust risk appetite based on strategic shifts.
- Ensure budget allocations reflect risk priorities.
Culture of Risk Awareness
Technology and processes are secondary to people. A culture where employees feel safe reporting risks is vital.
- Encourage open discussion about potential failures.
- Recognize teams that identify risks early.
- Train staff on how to spot and report threats.
🎯 Measuring Plan Effectiveness
How do you know the plan is working? Effectiveness is measured by the reduction in negative outcomes and the organization’s resilience.
Metrics for Success
- Reduction in Incident Frequency: Are the identified risks happening less often?
- Cost of Risk: Is the financial impact of incidents decreasing?
- Response Time: How quickly is the team reacting to emerging threats?
- Stakeholder Confidence: Do investors or partners feel secure in the organization’s stability?
🔄 Continuous Improvement
The landscape of business is dynamic. A risk management plan derived from SWOT threats must evolve. As new information becomes available, the plan must be updated.
- Conduct post-incident reviews to learn from what happened.
- Update the SWOT analysis regularly to capture new external threats.
- Refine mitigation strategies based on what worked and what didn’t.
- Stay informed about industry trends and emerging risks.
By treating the Risk Management Plan as a living document, organizations can navigate uncertainty with confidence. The connection between the SWOT analysis and risk mitigation is the bridge between strategic vision and operational reality. When threats are identified, assessed, and managed systematically, the organization builds a foundation for sustainable growth and resilience.
📝 Final Thoughts on Strategic Defense
Building a plan based on SWOT threats is not about fear; it is about preparation. It allows leaders to make informed decisions rather than reactive ones. By following the steps outlined in this guide, teams can ensure that every threat identified in the initial analysis has a corresponding path forward. This discipline transforms vulnerability into a manageable variable within the broader strategic equation.
Remember, the goal is not to eliminate all risk, but to manage it effectively. With clear ownership, defined strategies, and regular monitoring, the organization can withstand external shocks and maintain its trajectory toward long-term success.