In the modern financial landscape, capital is abundant, but confidence is scarce. Investors are no longer satisfied with glossy projections and optimistic narratives. They demand clarity, especially when it comes to risk. The mechanism that bridges the gap between operational reality and investor expectations is the transparent threat assessment embedded within strategic planning frameworks like SWOT analysis. This guide explores how organizations can leverage vulnerability to build credibility.
Trust is not granted; it is earned through consistent behavior and honest reporting. When a company openly acknowledges potential threats, it signals maturity. It shows leadership understands the environment they operate in. This document details the process of integrating threat assessment into your strategic narrative without resorting to fear-mongering or minimization.
Why Transparency Matters in Capital Markets 💰
Historically, negative information was often buried until it became a crisis. Today, information asymmetry is a liability. Investors utilize due diligence processes that scrutinize every aspect of a business model. If a company hides a significant weakness or threat, the moment that information surfaces, the cost of recovery is exponentially higher than the cost of early disclosure.
Transparency serves several critical functions in the investor relationship:
- Risk Calibration: It allows investors to price risk accurately. Hidden risks lead to mispricing, which eventually corrects violently.
- Partnership Building: It shifts the dynamic from “principal-agent” to genuine partnership. Investors become allies in mitigation rather than adversaries in discovery.
- Reputation Management: Proactive disclosure establishes a track record of honesty. Future issues are viewed through the lens of past transparency.
- Regulatory Alignment: Many jurisdictions now require specific risk disclosures. Being ahead of these requirements demonstrates governance competence.
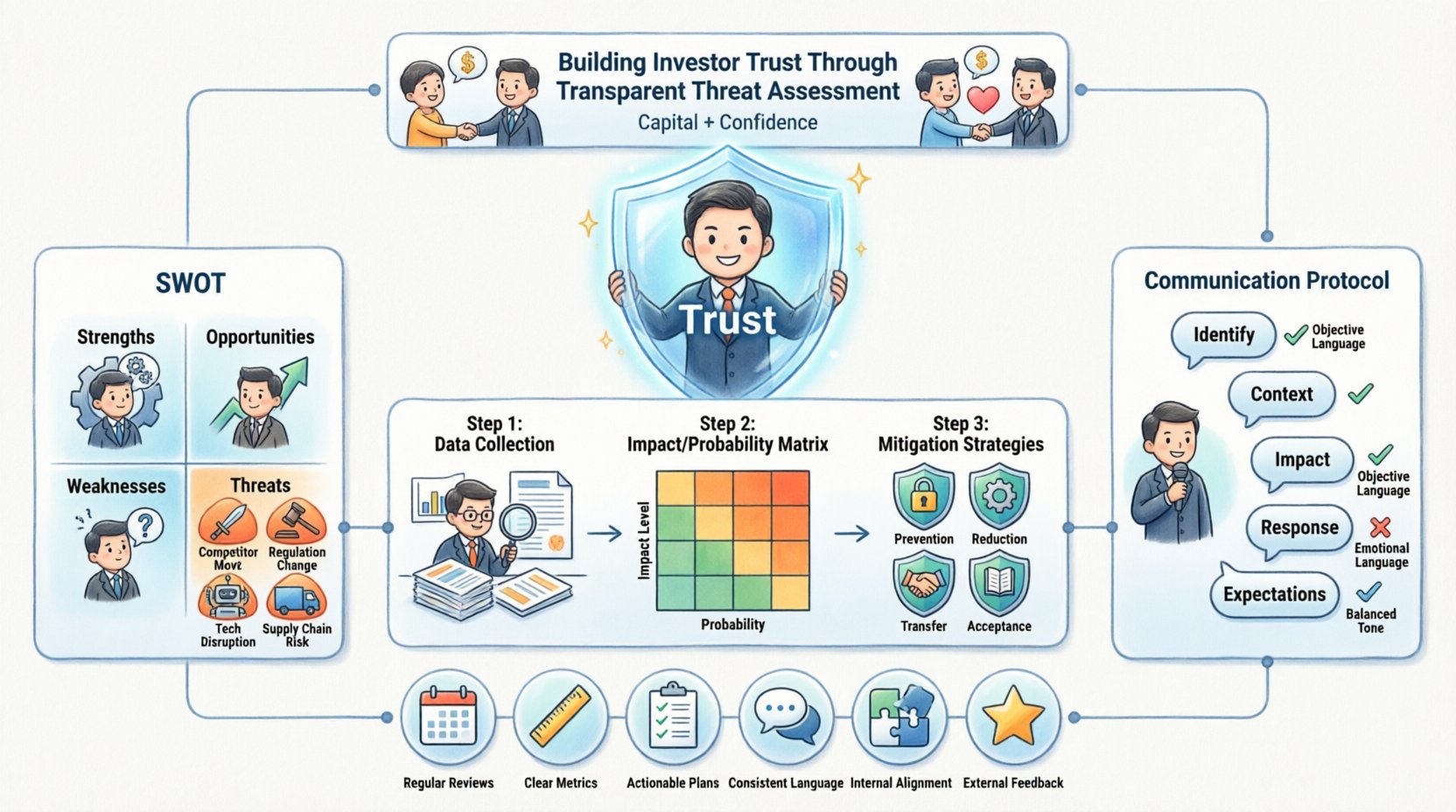
The SWOT Framework Revisited: Focusing on Threats 🧩
SWOT analysis (Strengths, Weaknesses, Opportunities, Threats) is a standard tool, yet it is often executed superficially. For investor relations, the “Threats” and “Weaknesses” quadrants require the most rigorous attention. These are the areas where trust is most often tested.
Defining Threats in a Business Context
A threat is an external factor that could cause trouble for the business. Unlike weaknesses, which are internal, threats exist in the market, regulatory environment, or supply chain. However, the response to a threat is internal.
Common categories of threats include:
- Market Shifts: Changes in consumer behavior or demand volatility.
- Competitive Pressure: New entrants or price wars initiated by rivals.
- Regulatory Changes: New laws affecting operations or compliance costs.
- Technological Disruption: Obsolescence of current technology stacks.
- Supply Chain Fragility: Dependency on single-source vendors or geopolitical instability.
Mapping Threats to Investor Concerns
Investors do not just want a list of problems; they want to see the correlation between those problems and financial performance. The following table illustrates how specific threats translate into investor metrics.
| Threat Category | Investor Concern | Disclosure Metric |
|---|---|---|
| Regulatory Compliance | Liability Exposure | Cost of Compliance vs. Revenue |
| Supply Chain Disruption | Margin Volatility | Inventory Turnover Ratios |
| Competitive Entry | Market Share Loss | Customer Churn Rates |
| Technological Obsolescence | Asset Write-downs | R&D Spend as % of Revenue |
Methodology: Conducting a Rigorous Threat Assessment 📊
To build trust, the assessment process must be robust. It cannot rely on gut feelings or optimistic assumptions. It requires a structured approach to data gathering and analysis.
Step 1: Data Collection and Validation
Gathering data from multiple sources ensures a holistic view. Relying on internal reports alone creates blind spots. External market data, competitor analysis, and customer feedback loops are essential.
- Internal Data: Review past incident reports, audit findings, and operational bottlenecks.
- External Intelligence: Monitor industry reports, regulatory filings of competitors, and macroeconomic indicators.
- Stakeholder Interviews: Engage with operational teams, not just executive leadership, to identify ground-level risks.
Step 2: Impact and Probability Scoring
Not all threats are created equal. Some are likely but minor; others are catastrophic but rare. A scoring matrix helps prioritize which threats require immediate investor communication.
- High Probability / High Impact: These require immediate mitigation strategies and full disclosure.
- Low Probability / High Impact: These are insurance scenarios. Disclose the existence of the risk and the contingency plan.
- High Probability / Low Impact: These are operational nuisances. Address them in standard operational reports.
- Low Probability / Low Impact: These are monitored but do not warrant detailed investor memos.
Step 3: Developing Mitigation Strategies
Identifying a threat is only half the job. The value lies in the solution. Investors want to see that the organization has a plan B.
- Prevention: Actions taken to stop the threat from occurring.
- Reduction: Actions taken to minimize the impact if it occurs.
- Transfer: Insurance or hedging strategies to shift financial risk.
- Acceptance: Acknowledging the risk and budgeting for the potential loss.
Communication Protocols for Investor Relations 📢
How you deliver the information is as important as the information itself. The tone should be factual, measured, and forward-looking. Avoid language that suggests panic or defensiveness.
The Structure of a Risk Disclosure
When communicating threats, follow a consistent structure to ensure clarity and comparability over time.
- Identify the Risk: State clearly what the threat is.
- Explain the Context: Why does this matter now? What triggered this assessment?
- Assess the Financial Impact: Provide ranges or estimates of potential financial effect.
- Outline the Response: Detail the steps being taken to manage the situation.
- Set Expectations: Indicate how progress will be tracked and reported in the future.
Language and Tone Guidelines
Word choice influences perception. Using precise terminology reduces ambiguity.
- Avoid: “We are worried about…” (Emotional)
- Use: “We are monitoring a trend…” (Objective)
- Avoid: “This will destroy our margins.” (Sensationalist)
- Use: “This may reduce margins by 2-5% under current conditions.” (Quantified)
- Avoid: “We have it under control.” (Dismissive)
- Use: “We have implemented controls to mitigate exposure.” (Action-oriented)
Handling Negative Findings Without Panic 🧱
It is common to feel a hesitation to share negative findings. However, hiding a weakness until it becomes a crisis is the fastest way to destroy trust. The goal is to normalize the discussion of risk.
Normalizing Risk in Quarterly Reports
Do not reserve risk discussions only for annual reports. Incorporate them into quarterly updates. This prevents surprises. If a specific threat materializes, it should feel like a known variable, not a new shock.
- Consistency: Use the same risk categories every quarter.
- Progress Tracking: Show if the risk level has increased, decreased, or stayed the same.
- Action Updates: Report on the status of mitigation plans from the previous quarter.
The “Bad News First” Approach
In certain contexts, presenting the challenge before the solution can demonstrate leadership confidence. It shows you are not waiting for the question to be asked.
Example Statement: “While our revenue grew by 10%, we must note a 15% increase in supply chain costs. We are actively renegotiating vendor contracts to stabilize these figures in the next fiscal year.”
Common Pitfalls in Threat Assessment 🚫
Even with the best intentions, organizations can stumble in their assessment process. Recognizing these pitfalls helps maintain the integrity of the data.
Pitfall 1: Groupthink
When a leadership team agrees too quickly on the absence of risk, the assessment is flawed. Encourage dissenting opinions during the internal review phase. This ensures that potential threats are not overlooked due to optimism bias.
Pitfall 2: Static Assessment
A SWOT analysis is not a one-time event. Markets change. A threat assessment performed six months ago may be obsolete today. Maintain a living document that is updated regularly.
Pitfall 3: Overwhelming Detail
Investors do not want to read a 50-page risk register. Summarize key risks and provide a mechanism for accessing deeper details if needed. Focus on the risks that materially affect valuation.
Pitfall 4: Vague Mitigation Plans
Saying “we will monitor” is insufficient. Investors need to know who is monitoring, how often, and what triggers an escalation. Specificity breeds confidence.
Integrating Threat Data into Strategic Planning 🔄
Threat assessment should not exist in a silo within the Investor Relations department. It must feed directly into strategic planning. If a threat is identified, resources should be allocated to address it.
Budgeting for Risk
Allocate specific budget lines for risk mitigation. This demonstrates that the organization treats risk as a cost of doing business, not an afterthought.
- Contingency Funds: Set aside reserves for high-impact threats.
- Insurance Premiums: Adjust coverage based on the threat assessment.
- Technology Upgrades: Invest in systems that reduce operational risk.
Strategic Pivot Readiness
When a threat becomes existential, the strategy must pivot. Investors appreciate agility. If the assessment indicates that a core market is shrinking, the plan should outline the transition to a new market or product line.
Building a Culture of Accountability 🤝
Transparency requires a culture where employees feel safe reporting issues. If the internal culture punishes bad news, the external reporting will be sanitized and untrustworthy.
Internal Incentives
Align incentives so that identifying risks is rewarded, not penalized. Encourage cross-functional teams to collaborate on risk identification.
- Recognition: Acknowledge teams that identify critical risks early.
- Training: Provide training on risk recognition and reporting protocols.
- Channels: Establish anonymous or direct channels for reporting concerns.
The Long-Term Value of Honest Reporting 📈
The benefits of transparent threat assessment extend beyond the immediate investment cycle. It builds a brand of integrity that attracts long-term capital.
Attracting Patient Capital
Investors who focus on long-term value creation prefer companies with clear risk profiles. They are willing to accept short-term volatility if the long-term trajectory is understood and managed. Transparency filters for the right type of shareholder.
Reducing Cost of Capital
When risk is understood and managed, the uncertainty premium decreases. Lenders and investors may offer better terms because the perceived risk is lower. This directly impacts the bottom line.
Resilience in Crises
When a true crisis hits, companies with a history of transparency are given the benefit of the doubt. The narrative is already established. The organization can focus on solving the problem rather than defending its honesty.
Summary of Best Practices ✅
To summarize, building trust through transparent threat assessment requires discipline and consistency. The following checklist serves as a quick reference for maintaining high standards.
- Regular Reviews: Conduct threat assessments quarterly.
- Clear Metrics: Quantify risks wherever possible.
- Actionable Plans: Always pair a threat with a mitigation strategy.
- Consistent Language: Use standardized terminology in reports.
- Internal Alignment: Ensure all departments are aware of the risks.
- External Feedback: Solicit feedback from investors on the clarity of disclosures.
Final Thoughts on Strategic Honesty 🌟
The path to investor trust is paved with facts, not promises. By treating threat assessment as a core component of strategic planning rather than a compliance exercise, organizations can foster deeper relationships with their stakeholders. The goal is not to eliminate all risk, but to manage it in a way that is visible and understandable. When investors see the full picture, they are more likely to support the journey, even when the road becomes difficult.
This approach transforms the SWOT analysis from a static document into a dynamic tool for governance. It ensures that the organization remains agile and honest. In an era where information is ubiquitous, the most valuable asset a company can offer is its own integrity.


